Only 22.3% of global e-waste generated in 2022 was formally recycled, despite 62 million tonnes being produced worldwide that year. The rest was either landfilled, incinerated, or handled through informal channels that expose organizations to serious data security and regulatory risks. For IT managers and environmental compliance officers, this is not an abstract statistic. It represents the gap between what organizations think they are doing with retired equipment and what is actually happening. This guide walks through exactly what responsible IT disposal means, the steps required to do it right, the regulatory landscape you cannot afford to ignore, and the best practices that separate high-performing programs from those quietly accumulating risk.
Table of Contents
- Defining responsible IT disposal: Secure, compliant, and eco-friendly
- Key steps for compliant IT asset disposition
- Regulatory pressures and standards: Why compliance matters
- Best practices: Maximizing security and sustainability
- Why traditional IT disposal fails: Hard-won lessons and missed opportunities
- Partnering for responsible IT disposal: Next steps with E-waste Logistics
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Secure and compliant disposal | IT asset disposition protects data, meets regulatory obligations, and prevents costly breaches. |
| Environmental responsibility | Certified e-waste recycling preserves resources and reduces your organization’s carbon footprint. |
| Stepwise disposal process | Following best practices from inventory to certified recycling or destruction ensures security and sustainability. |
| Vendor oversight matters | Auditing partners and requiring relevant certifications is vital for transparency and compliance. |
Defining responsible IT disposal: Secure, compliant, and eco-friendly
Responsible IT disposal is not just about getting old hardware off your floor. It is a formal discipline known as IT Asset Disposition, or ITAD. ITAD is defined as the secure, compliant, and environmentally responsible process for retiring end-of-life IT equipment, covering data sanitization, value recovery, recycling, and physical destruction. That four-part definition matters because each element carries its own set of obligations, risks, and opportunities.
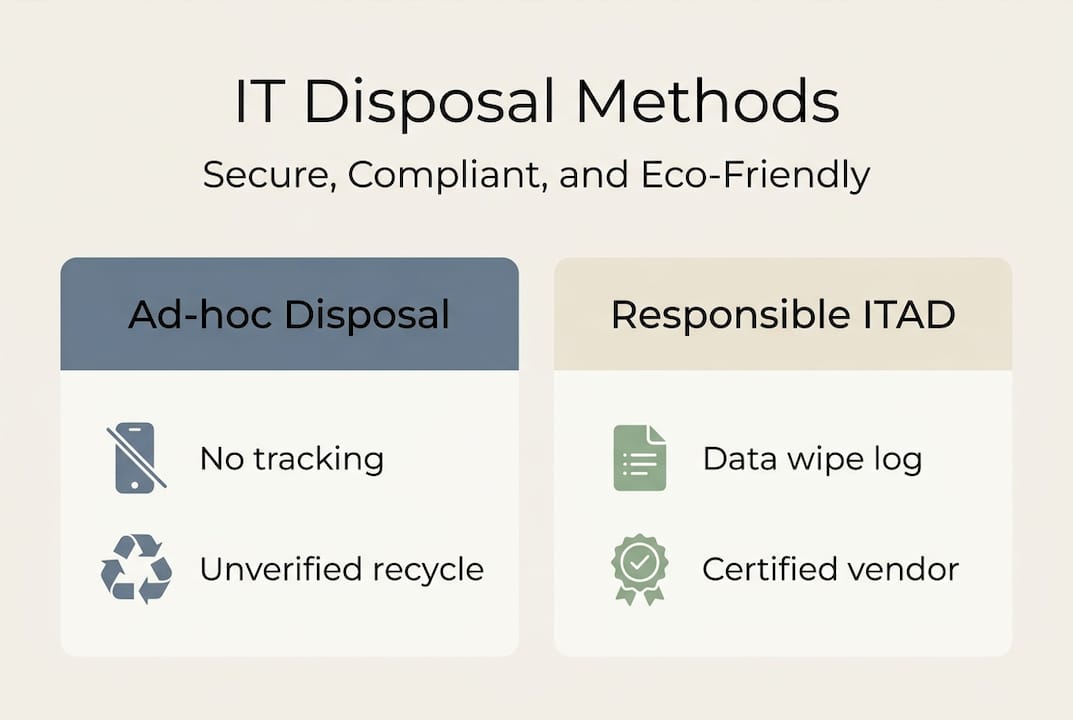
Too many organizations treat equipment retirement as a facilities management problem rather than an IT governance responsibility. A department head arranges for a vendor to pick up old laptops. No formal data wipe is performed. No certificate of destruction is issued. No chain of custody is documented. That is ad-hoc disposal, and it creates exposure that can persist for years after the hardware leaves the building.
Responsible IT asset disposal, by contrast, treats every retiring device as a controlled asset until it is formally decommissioned. It involves clearly assigned ownership, documented processes, and third-party verification at each stage. The core principles are:
- Data security: Every device must be sanitized before it leaves your custody, regardless of its destination.
- Regulatory compliance: Disposal methods must satisfy applicable federal, state, and international frameworks.
- Environmental responsibility: Devices must be routed through certified channels that prevent toxic materials from entering landfill.
- Value recovery: Functional components, resalable devices, and recoverable materials represent real financial return that most organizations leave on the table.
| Element | Ad-hoc disposal | Responsible ITAD |
|---|---|---|
| Data sanitization | Rarely documented | NIST-aligned, certified |
| Chain of custody | Informal or absent | Tracked and audited |
| Environmental routing | Unknown | Certified recycler only |
| Value recovery | Typically zero | Resale or materials credit |
| Compliance documentation | None | Certificate of destruction |
Pro Tip: Before any device moves off-site, confirm that your internal IT team or your ITAD vendor has completed a formal sanitization step and issued a documented record. That record is your legal protection if a data incident is later alleged to involve a retired device.
When preparing devices for secure recycling, organizations often discover that a surprising number of devices still hold active credentials, encryption keys, or cached network configurations. A structured ITAD program catches these before they become incidents.
Key steps for compliant IT asset disposition
Understanding the principles is one thing. Executing them consistently across hundreds or thousands of devices is another challenge entirely. Here is a process that holds up under audit pressure.
Step 1: Comprehensive inventory assessment. Start by cataloging every device scheduled for retirement. Record the make, model, serial number, data classification level of any information stored, and the physical condition of each unit. This inventory drives every downstream decision, including whether a device is eligible for resale, should be refurbished, or requires destruction. Organizations that skip this step routinely misplace assets, underreport value recovery, and expose themselves to audit failures.
Step 2: Data sanitization using NIST SP 800-88 guidelines. NIST SP 800-88 defines three sanitization categories: Clear (overwrite-based methods for lower-risk media), Purge (cryptographic erase or degaussing for higher-risk scenarios), and Destroy (physical shredding or crushing for devices that cannot be sanitized any other way). Matching the method to the data sensitivity level is critical. A solid-state drive that held health records requires a different treatment than a display monitor. Applying the wrong method creates either unnecessary cost or inadequate protection.

Step 3: Chain-of-custody tracking. From the moment a device is flagged for retirement, every handoff must be logged. Who collected it, when, where it went, and what happened to it. This is not bureaucratic overhead. It is the paper trail that proves compliance if you are audited, sued, or investigated. Many organizations use asset management software to automate this tracking, but even a rigorously maintained spreadsheet is better than informal handoffs.
Step 4: Certified disposal via audited partners. Physical removal and final processing must be handled by a vendor that holds recognized certifications. Secure equipment recycling processes carried out by certified partners provide the downstream transparency your compliance team needs. Look for R2v3 or e-Stewards certification as minimum qualification criteria.
Step 5: Certificate of destruction and final reporting. At program close, you should receive a formal certificate of destruction for every device sanitized or destroyed, a downstream tracking report for recycled materials, and a value recovery statement for any assets resold. This documentation package is what converts a disposal event into a defensible compliance record.
| Sanitization method | NIST category | Best for | Risk level addressed |
|---|---|---|---|
| Overwrite (software) | Clear | HDDs, lower-risk data | Low to medium |
| Cryptographic erase | Purge | SSDs, encrypted drives | Medium to high |
| Degaussing | Purge | Magnetic media | High |
| Physical shredding | Destroy | All media, highest risk | Maximum |
NIST-aligned data destruction is not optional for organizations handling regulated data. It is the baseline that regulators expect to see documented in your records.
Pro Tip: Match your sanitization tier to your data classification policy. Devices that touched personally identifiable information, payment card data, or protected health information should receive Purge or Destroy-level treatment, even if they appear wiped. Overwrite alone is not sufficient for high-sensitivity media.
Regulatory pressures and standards: Why compliance matters
The regulatory landscape for IT disposal has grown significantly more complex over the past decade. Multiple overlapping frameworks now govern how organizations must handle end-of-life equipment and the data stored on it.
Key frameworks include:
- NIST SP 800-88: The technical standard for data sanitization referenced by most U.S. federal agencies and widely adopted by the private sector.
- WEEE Directive (EU): Requires producers and handlers to meet a 65% collection target for electronic equipment. Organizations operating in EU markets must ensure their disposal channels meet WEEE compliance requirements.
- EPA e-waste rules: U.S. Environmental Protection Agency regulations govern the handling of hazardous materials present in electronic equipment, including lead, mercury, and cadmium.
- GDPR: Applies to any organization handling EU resident data, regardless of geography. Improper disposal of data-bearing media can trigger fines reaching €20 million or 4% of global annual turnover, whichever is greater.
- HIPAA: Requires covered entities and business associates to implement policies for the final disposition of electronic protected health information, including documentation of the methods used.
Compliance reality check: GDPR and HIPAA fines are not theoretical. Regulators have levied multimillion-dollar penalties against organizations whose disposal practices left personal data recoverable on resold or discarded devices. The cost of a proper ITAD program is a fraction of the cost of a single enforcement action.
Regular internal audits of your disposal practices are not just good governance. They are the mechanism that keeps your program aligned with frameworks that evolve. When a regulation updates its guidance on acceptable sanitization methods, organizations without formal audit cycles are usually the last to know and the first to get cited.
Working with certified e-waste standards ensures that your vendor’s downstream practices meet the environmental requirements attached to these frameworks. Certification is verifiable. Promises are not.
Best practices: Maximizing security and sustainability
Once you have a compliant baseline, the next step is building a program that delivers measurable value beyond just avoiding fines. High-performing organizations treat ITAD as a strategic function that generates both risk reduction and financial return.
Centralize ITAD under standardized policy. Decentralized disposal, where individual departments or locations manage their own equipment retirement, is one of the most common sources of program failure. Approximately 70% of data breaches attributable to ITAD failures are preventable through proper centralized policies with automated tracking and annual vendor audits. Centralizing means one policy, one approved vendor list, one documentation standard, and one reporting mechanism.
Audit vendors annually. Certifications are a starting point, not a permanent guarantee. R2v3 and e-Stewards certifications require ongoing audits, but your own vendor review process should confirm that practices match what is documented. Ask for downstream tracking reports. Request facility inspection access. Treat your ITAD vendor the way you treat any other critical supplier in your risk management program.
Measure environmental impact. Sustainability metrics matter to boards, investors, and regulators. Recycling 1 million laptops saves enough energy to power approximately 3,500 U.S. homes for a year. That is the kind of figure that belongs in a corporate sustainability report, and it comes directly from the output of a well-run ITAD program. Track the volume of devices processed, the weight of materials diverted from landfill, and the energy equivalents of materials recovered.
| Performance metric | What to measure | Why it matters |
|---|---|---|
| Sanitization rate | % of devices with documented wipe | Compliance evidence |
| Value recovery | Dollar return per retired asset | Financial ROI visibility |
| Landfill diversion | kg of materials recycled vs. disposed | ESG reporting |
| Vendor audit score | Annual scorecard from vendor reviews | Supply chain risk management |
| Certification coverage | % of downstream handled by certified partners | Regulatory defensibility |
Prioritize Extended Producer Responsibility (EPR) frameworks. 25 U.S. states have enacted EPR legislation that places legal responsibility on producers and handlers for the end-of-life management of electronics. Compliance officers in these states must map their ITAD program to specific reporting obligations. Staying ahead of EPR requirements in your operating states protects against sudden compliance gaps when legislation is enforced.
Eco-friendly IT asset recovery is not a compromise between security and sustainability. Done correctly, it achieves both simultaneously. Certified downstream partners provide chain-of-custody documentation for data security purposes while also routing materials through responsible recycling streams.
Pro Tip: Build ITAD into your hardware refresh cycle from the beginning, not as a cleanup step at the end. When procurement teams know that devices have a defined retirement path, asset tracking stays accurate, disposal costs become predictable, and your compliance posture stays strong throughout the device lifecycle. Reviewing computer recycling options at the time of purchase helps procurement teams select vendors and plan for responsible end-of-life management well in advance.
Why traditional IT disposal fails: Hard-won lessons and missed opportunities
Here is an uncomfortable truth about IT disposal: most organizations are not failing because they do not care. They are failing because they treat ITAD as an event rather than a system. A server reaches end-of-life. Someone calls a vendor. The vendor picks it up. The organization assumes the problem is solved. That sequence works fine until a breach investigation traces a data incident back to a device that was supposedly retired two years ago.
What separates genuinely resilient programs from the rest is not budget. It is discipline applied consistently. The organizations that handle ITAD well tend to share a few characteristics. They assign clear ownership. ITAD does not belong to facilities, IT, legal, or procurement exclusively. It sits at the intersection of all four, with a designated lead responsible for policy, vendor management, and reporting. They automate what they can. Manual tracking breaks down at scale. Automated asset management tools that flag devices when they reach end-of-life, trigger sanitization workflows, and generate documentation without human intervention remove the single biggest failure point in most programs.
They also treat value recovery seriously. Many IT managers are surprised to find that a structured resale and parts recovery program can offset a significant portion of ITAD operating costs. Devices that seem obsolete often contain components with real secondary market value. Ignoring this is not just leaving money on the table. It is also missing an opportunity to fund the program that keeps your data secure and your compliance record clean.
The missed opportunity is usually not dramatic. It is quiet. It is the audit that goes poorly because documentation was not maintained. It is the device that shows up in a secondary market with data still intact. Preventing those outcomes is exactly what a mature ITAD program, supported by the right partner, is designed to do. Securing lasting ITAD value requires treating disposition as a continuous operational function, not a one-time project.
Partnering for responsible IT disposal: Next steps with E-waste Logistics
Organizations that take ITAD seriously need more than good intentions. They need a partner with certified processes, documented chain of custody, and the operational capacity to handle volume consistently.
UsedCartridge.com delivers full-service responsible e-waste solutions that cover every stage of the IT asset lifecycle: secure pickup, NIST-aligned data destruction, certified recycling, value recovery reporting, and official certificates of destruction. Whether you are managing a single office refresh or a multi-site decommissioning project, the process is built around your compliance requirements. Explore business e-waste recycling options tailored to your sustainability and regulatory goals, or take the first step and get an ITAD quote customized to your organization’s needs. Responsible disposal is not a cost center. With the right partner, it is a risk management strategy that pays for itself.
Frequently asked questions
What are the main risks of not using responsible IT disposal?
The main risks are data breaches, regulatory fines, and environmental liability from improper e-waste handling. GDPR non-compliance alone can result in fines of up to €20 million or 4% of global annual turnover.
How can organizations ensure data is irretrievably destroyed during IT disposal?
Organizations should apply NIST SP 800-88 methods matched to data sensitivity, including overwriting for lower-risk media, cryptographic erase or degaussing for higher-risk drives, and physical shredding for maximum-risk scenarios.
Which certifications should vendors hold for responsible IT disposal?
Vendors should hold R2v3 or e-Stewards certification for recycling operations and demonstrate documented NIST SP 800-88 alignment for data destruction services. Both certifications require third-party audits.
What value can be recovered through responsible IT disposal?
Value recovery includes device resale, component harvesting, and materials recycling. Globally, formal recycling recovers $57 billion in materials value annually, with individual organizations often recovering meaningful offsets against their ITAD program costs.
Recommended
- Eco-Friendly IT Asset Recovery Tips for Compliance & ROI – E-waste Logistics
- Green E-Waste Management: Secure, Sustainable Practices – E-waste Logistics
- Secure Equipment Recycling: Protect Data and the Environment – E-waste Logistics
- Secure E-Waste Pickup: Protect Data & the Environment – E-waste Logistics
