Most organizations believe that handing off old computers and servers to a recycling vendor automatically protects their data. That assumption is wrong, and it has real consequences. Data breaches traced to improperly retired IT assets have cost businesses millions in regulatory fines and reputational damage. Secure equipment recycling is a fundamentally different process from basic e-waste drop-off. It combines data sanitization controls with strict chain-of-custody tracking and certified environmental disposal. This guide walks you through what secure equipment recycling actually requires, how the workflow is structured, and how to choose a provider that protects your organization at every step.
Table of Contents
- Understanding secure equipment recycling
- Key steps and controls in secure recycling workflows
- Sanitization standards, validation, and when device reuse is safe
- Choosing the right provider: Certifications, chain of custody, and compliance
- Why secure equipment recycling isn’t just IT’s job: Organizational lessons
- How we support secure recycling for your business
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| True secure recycling | Secure equipment recycling means verified data destruction, not just device removal. |
| Follow recognized standards | Using NIST and industry-certified providers ensures compliance and audit-readiness. |
| End-to-end controls | Effective workflows require documentation, chain-of-custody, and certified environmental processing. |
| Risk-based decisions | Choose between reuse or physical destruction based on asset risk and proper validation. |
Understanding secure equipment recycling
Secure equipment recycling is the controlled, end-of-life process for IT assets that covers three distinct requirements: data sanitization, chain-of-custody documentation, and responsible downstream recycling. Strip away any one of those three elements and you no longer have a secure process. You have a liability.
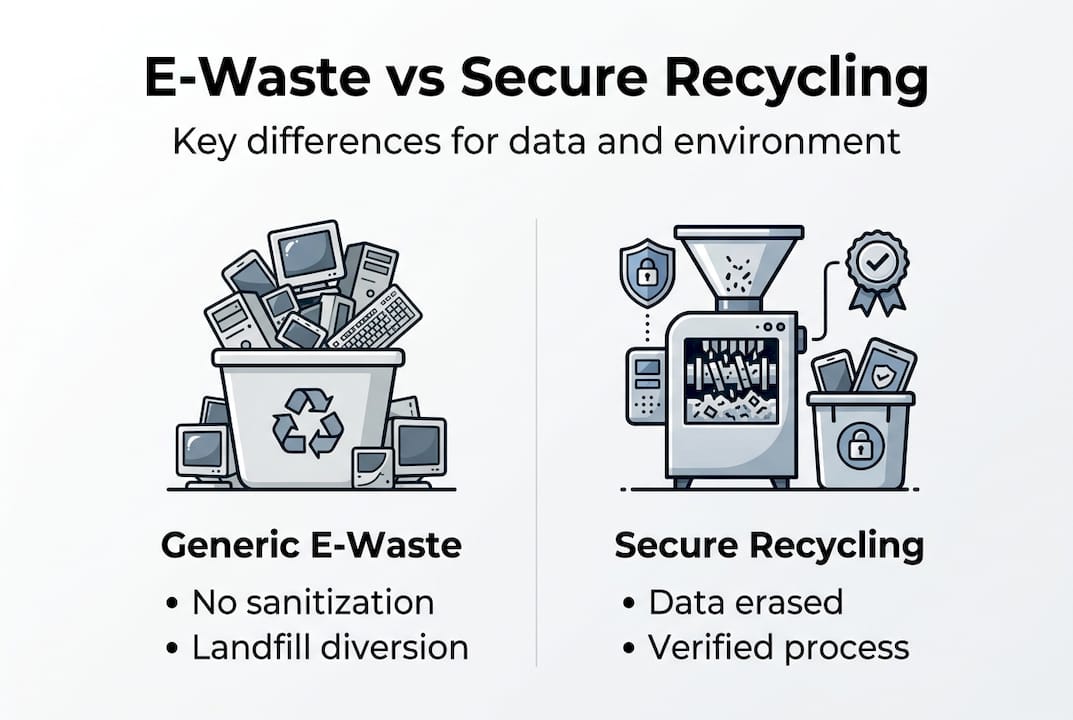
Generic e-waste recycling focuses primarily on diverting electronics from landfills. That goal matters, but it says nothing about what happens to the data still stored on drives, flash memory, or embedded chips. Secure equipment recycling, by contrast, is governed by sanitization standards that are specifically designed to address data risk alongside environmental responsibility.
The authoritative reference for sanitization requirements is NIST SP 800-88 Rev. 2, published by the National Institute of Standards and Technology. NIST guidelines require that controls render access to all data on a device completely infeasible before that device leaves an organization’s control. That standard applies regardless of whether the device is being reused, donated, or destroyed.
Here is a quick comparison of generic e-waste recycling versus secure equipment recycling:
| Feature | Generic e-waste recycling | Secure equipment recycling |
|---|---|---|
| Data sanitization | Not required | Mandatory, NIST-referenced |
| Chain of custody | None | Documented and auditable |
| Certificates of destruction | Rarely issued | Standard deliverable |
| Compliance support | None | Supports HIPAA, GDPR, SOX |
| Environmental controls | Basic | Certified downstream recycling |
When reviewing old equipment disposal steps at your organization, the absence of a sanitization record for any retired device is a red flag.
Key characteristics that define a secure recycling program include:
- Asset-level tracking from collection through final disposal
- NIST-validated sanitization applied to every storage medium
- Written chain-of-custody records signed at each transfer point
- Downstream vendor accountability for environmentally responsible processing
- Certificates of data destruction delivered to the client as audit evidence
“Secure equipment recycling requires controls that render access to all data infeasible.” This principle from NIST SP 800-88 Rev. 2 is the baseline for any program that claims to protect your organization.
Understanding this definition makes it easier to evaluate vendors, design internal policies, and respond confidently to auditors or regulators asking how your organization retires technology.
Key steps and controls in secure recycling workflows
Now that we’ve defined secure equipment recycling, let’s look at how these principles are applied in real-world business and IT workflows. The process follows five structured steps, and skipping even one creates gaps that auditors and regulators will find.
A mechanical process per NIST covers asset identification, secure logistics, data sanitization, verification, and certified environmental recycling. Here is how each step works in practice:
-
Asset inventory. Before any device leaves your building, every unit is cataloged. Serial numbers, device types, storage media, and assigned users are recorded. This creates the baseline your audit trail depends on.
-
Secure logistics. Equipment moves under controlled conditions. Sealed, tamper-evident containers and tracked transportation prevent unauthorized access between collection and processing. For high-sensitivity organizations, on-site processing eliminates transport risk entirely.
-
Data sanitization. The right method is applied to each device based on media type, classification level, and downstream intent. More on choosing the correct method appears in the next section.
-
Verification and validation. Every sanitized device is checked to confirm the process succeeded. Automated logs capture outcomes for each unit. This documentation becomes the evidence your compliance team needs.
-
Certified downstream recycling. After data is addressed, materials are processed through a certified recycler. This step ensures hazardous components like lead and mercury are handled properly and kept out of landfills.
The equipment destruction process and secure computer recycling both follow this five-step model when executed by a qualified ITAD provider.

Process documentation is what separates defensible compliance from wishful thinking. Certificates of destruction, sanitization logs, and chain-of-custody records give your legal and compliance teams concrete evidence to present during audits or in response to regulatory inquiries. Aligning these records with your IT asset management practices makes the entire process sustainable across equipment refresh cycles.
Pro Tip: Request sample documentation from any recycling vendor before signing a contract. If they cannot show you a sample certificate of destruction and sanitization log within minutes, assume those records do not exist.
Sanitization standards, validation, and when device reuse is safe
Understanding the workflow, it’s crucial to choose the right sanitization method, and know when each is appropriate. NIST SP 800-88 Rev. 2 defines three primary approaches, and the correct choice depends on media type, data sensitivity, and whether the device will be reused.
Here is a comparison of the three main sanitization methods:
| Method | Best for | Reuse possible? | Validation method |
|---|---|---|---|
| Software wiping | HDDs, low-sensitivity data | Yes | Automated logs |
| Cryptographic erase | SSDs, self-encrypting drives | Yes | Encryption key deletion record |
| Physical destruction | High-sensitivity, unrecoverable media | No | Certificate of destruction |
NIST models require rendering data access infeasible and validating outcomes for each asset or batch. That validation piece is non-negotiable. A wipe that was interrupted, applied to the wrong drive, or performed by outdated software leaves recoverable data behind. Without a log confirming success, you cannot prove compliance.
Cryptographic erase has become increasingly important as SSDs replace traditional hard drives. When a self-encrypting drive has its encryption key deleted, the stored data becomes permanently inaccessible without physically destroying the device. This makes reuse practical for modern hardware while still meeting regulatory standards.
The decision between reuse and destruction involves several factors:
- Regulatory environment. Healthcare organizations under HIPAA often require destruction for certain media types regardless of sanitization.
- Drive condition. Damaged or failing drives should always be destroyed. Attempting to wipe a failing drive risks leaving recoverable data.
- Downstream destination. A device being resold internally faces different standards than one being donated externally.
Pro Tip: If your organization uses full-disk encryption as a standard policy, cryptographic erase is fast, cost-effective, and fully NIST-compliant for most reuse scenarios.
Reviewing sanitization methods for devices before a major equipment refresh gives your IT team a clear decision framework before assets leave the building. For situations requiring physical destruction, the physical destruction option provides on-site shredding with documented outcomes. For organizations standardizing their overall approach, NIST implementation details help frame the right policies.
Choosing the right provider: Certifications, chain of custody, and compliance
Selecting the best recycling method is only one part. The right provider ensures those standards are rigorously followed every time, not just on paper.
Secure recycling via ITAD providers uses NIST-referenced practices and demonstrates controls through certifications like R2. When evaluating vendors, ask these questions directly:
- What sanitization methods do you use, and which NIST categories do they address?
- How is chain of custody documented from asset pickup through final processing?
- What certifications does your facility hold, and are they current?
- What does your certificate of destruction include, and how quickly is it delivered?
- How are subcontractors or downstream vendors vetted?
Here is a quick-reference table mapping key certifications to their coverage areas:
| Certification | Data security controls | Environmental safeguards | Worker safety | Third-party audited |
|---|---|---|---|---|
| R2 (Responsible Recycling) | Yes | Yes | Yes | Yes |
| e-Stewards | Yes | Yes | Yes | Yes |
| ISO 27001 | Yes | No | No | Yes |
| NAID AAA | Yes | No | No | Yes |
Provider compliance does more than satisfy auditors. It shifts liability. When a certified ITAD provider fails to sanitize a device and data leaks, your organization’s documented due diligence in selecting and managing that vendor provides critical legal protection. Without it, your organization absorbs the full regulatory risk.
For businesses seeking IT asset disposition services, the provider’s certifications should appear in the service agreement and be verifiable through the certifying body’s public registry. Don’t accept verbal assurances. Require documentation.
For organizations with specialized hardware, secure recycling for batteries and other components requires providers with specific environmental certifications beyond standard ITAD scope. The R2 certification overview explains exactly what controls that standard enforces, making it a useful benchmark for evaluating any vendor’s claims.
Why secure equipment recycling isn’t just IT’s job: Organizational lessons
Here is something most IT-focused guides skip entirely: a significant portion of data exposure events tied to retired equipment trace back to decisions made outside the IT department. Finance teams authorizing equipment sales without flagging drives for sanitization. HR departments donating old laptops as a goodwill gesture. Facility managers clearing out server rooms during a lease transition without notifying IT.
These are not malicious acts. They are well-intentioned mistakes made by people who were never taught that a documented sanitization program is what separates compliance from exposure. Security and privacy compliance result from formal programs, not assumptions about what recycling vendors will handle automatically.
Treating secure equipment recycling as a company-wide responsibility, not just an IT checklist, changes the risk profile entirely. Procurement needs to know what happens to a device at end-of-life before they approve the purchase. Finance needs to understand that residual value recovery from old assets must go through a secure channel, not a quick auction. HR needs a clear policy before donating equipment to schools or nonprofits.
Building this culture is ultimately about defensibility. When a regulator asks how your organization manages data on retired assets, the right answer involves cross-departmental accountability, not just a vendor contract. Your ITAD program insights should reflect that breadth from day one.
How we support secure recycling for your business
If you’re ready to simplify and secure your equipment recycling, our expert team can help at every stage of the process.
At UsedCartridge.com, we manage the full lifecycle from scheduled asset pickup and documented chain-of-custody handling to NIST-aligned sanitization and certified destruction. Our clients receive certificates of destruction and sanitization logs that satisfy HIPAA, GDPR, SOX, and other regulatory requirements. Every step is designed to eliminate guesswork and give your compliance team the evidence they need. Whether you need to retire a single server or manage a full fleet refresh, our e-waste recycling solutions and equipment destruction services are built around your security and environmental obligations. Request a free quote today and find out how straightforward secure recycling can be.
Frequently asked questions
What makes equipment recycling ‘secure’ for businesses?
Secure equipment recycling ensures all data is rendered inaccessible through NIST-defined sanitization controls and tracks every device with auditable chain-of-custody documentation and certified environmental disposal.
How do I know if my company is compliant with data disposition regulations?
Compliance is demonstrated through NIST-referenced sanitization records, validation logs, and certificates of destruction from a documented, validated program managed by a certified ITAD partner.
Do I have to destroy every device, or can some be reused safely?
Devices can be reused when a NIST-validated sanitization method such as cryptographic erase or verified software wiping is applied and the outcome is documented.
What certifications should a recycling provider have?
Prioritize providers with R2 certification, which requires verified data sanitization controls, environmental compliance, and worker safety standards enforced through third-party audits.
