The majority of discarded electronics never reach certified recycling streams. In fact, only up to 25% of e-waste is formally collected even in countries with established systems, leaving the rest exposed to data breaches, toxic mishandling, and regulatory risk. For IT professionals managing large device fleets, that gap is not an abstraction. It is a liability. This guide cuts through the complexity of green e-waste management, explaining how frameworks like ITAD and EPR work together, what secure data destruction actually requires, and how to evaluate vendors so your organization stays compliant, sustainable, and protected.
Table of Contents
- Understanding green e-waste management: Principles and frameworks
- Regulations and Extended Producer Responsibility: Compliance essentials
- Secure data destruction: Protecting privacy in e-waste streams
- Choosing certified vendors and performance benchmarks
- What most IT leaders miss about green e-waste management
- Take the next step: Secure sustainable e-waste solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Prioritize secure ITAD | Always integrate data sanitization and chain-of-custody before any form of e-waste processing. |
| Regulatory compliance drives results | Countries enforcing EPR show significantly higher collection and eco-design adoption. |
| KPIs must go beyond weight | True recovery measures material reuse and closed-loop outcomes, not just weight-based statistics. |
| Certified partners matter | Choosing vendors with verifiable credentials ensures high recovery rates and regulatory compliance. |
Understanding green e-waste management: Principles and frameworks
Green e-waste management is not just recycling. It is a structured approach to extending the life of IT assets, securing sensitive data, and ensuring that end-of-life devices are processed with minimal environmental and legal risk. Think of it as applying the same rigor you give to cybersecurity policy to the physical exit of every device that ever touched your network.
The foundation is the waste hierarchy, a priority-ordered approach that runs: reduce, reuse, recycle, and responsible disposal. In IT terms, this means repairing or refurbishing devices before retiring them, redeploying equipment internally or donating it, recycling components that cannot be reused, and only then disposing of what remains through certified channels. The waste hierarchy and secure data sanitization form the backbone of any effective IT Asset Disposition (ITAD) strategy.
ITAD, or IT Asset Disposition, is the formal process for retiring IT equipment in a way that protects data and recovers value. It integrates data sanitization standards like NIST 800-88 (the federal guideline for media sanitization) and NAID AAA certification (the industry standard for data destruction service providers). Before any device leaves your control, these standards define how drives must be wiped, overwritten, or physically destroyed.
For an overview of e-waste management and the types of e-waste your organization may encounter, it helps to understand how green and conventional approaches differ:
| Factor | Green e-waste management | Conventional disposal |
|---|---|---|
| Data handling | NIST 800-88 / NAID AAA certified | Often undocumented |
| Device fate | Refurb, reuse, then recycle | Direct disposal or export |
| Documentation | Chain-of-custody certificates | Minimal or none |
| ESG alignment | Supports Scope 3 reporting | No structured tracking |
| Regulatory risk | Low (auditable) | High (potential violations) |
Key principles every IT organization should follow:
- Inventory all assets before initiating any disposition process
- Classify data sensitivity at the device level, not just by asset type
- Prioritize refurbishment before retiring devices to maximize value recovery
- Engage only vendors who provide verifiable downstream documentation
Pro Tip: Request a sample certificate of data destruction from any ITAD vendor before signing a contract. If they cannot produce one immediately, that is a red flag.
Partnering with a provider offering secure IT asset recovery ensures that these principles are operationalized, not just aspirational.
Regulations and Extended Producer Responsibility: Compliance essentials
With the foundational frameworks in place, it is important to understand the regulatory landscape and how compliance drives real-world results. E-waste regulation is no longer a regional concern. It is a global compliance challenge that directly affects how IT departments retire assets across multi-site operations.
Extended Producer Responsibility (EPR) is the regulatory model that shifts end-of-life management costs onto manufacturers, importers, and, by extension, the organizations that deploy their products. EPR is now enforced in 67 countries globally, with collection rates reaching up to 25% where formal systems are in place. That may sound low, but it is a significant jump compared to regions without any EPR framework.

Here is what the data looks like across regulatory contexts:
| Regulatory status | Typical collection rate | Data security requirements |
|---|---|---|
| EPR enforced | Up to 25% | Varies by country |
| No formal EPR | Below 5% | Often none |
| US state-level laws | 10-20% (varies) | FISMA, state privacy laws |
| EU WEEE Directive | 35-65% | GDPR aligned |
For US-based organizations, compliance does not stop at federal law. Many states have individual e-waste recycling mandates. Failing to track device disposition across state lines can expose your organization to penalty under multiple frameworks simultaneously.
Key compliance actions for IT decision-makers:
- Map your device footprint by jurisdiction before planning any disposal cycle
- Verify that vendors are EPR-registered in each state or country where collection occurs
- Document everything: manifests, certificates, and weight tickets are non-negotiable
- Track compliance with frameworks like FISMA and CMMC for federal contractors
Guidance on proper e-waste recycling can help your team stay ahead of evolving mandates. For a full look at how business sustainability and compliance interact in practice, the distinction between stated policy and auditable process matters far more than most IT leaders realize.
Key stat: Organizations in EPR-enforced regions recycle at rates 5x higher than those without formal systems, according to the ITU’s 2025 global e-waste report.
Secure data destruction: Protecting privacy in e-waste streams
Beyond regulatory compliance, organizations must ensure sensitive data is protected throughout the asset life cycle. The risk does not end when a device leaves the building. It ends only when verified, documented destruction is complete.
Here is a structured approach to secure data destruction:
- Inventory and classify assets. Create a full asset register with serial numbers, data sensitivity levels, and assigned users before any device moves.
- Establish chain-of-custody. Every transfer, from desk to warehouse to vendor, must be logged. Gaps in custody documentation create audit vulnerabilities.
- Select the right destruction method. Functioning drives can be wiped using NIST 800-88-compliant software overwriting. Damaged or legacy drives require physical destruction such as degaussing (using a powerful magnetic field to erase data) or industrial shredding.
- Address legacy media separately. Tapes, optical drives, and older magnetic storage require degaussing or shredding because standard software methods do not work on all media types.
- Obtain a certificate of destruction. This document is your legal proof. It should include the destruction method, date, technician ID, and a serialized asset list.
- Audit your vendor. Confirm NAID AAA certification and ask for a process walkthrough or on-site inspection option.
“Chain-of-custody integrity is not a formality. For organizations subject to FISMA, CMMC, or state-level privacy laws, it is an auditable requirement with real penalties attached.”
Pro Tip: On-site data destruction eliminates chain-of-custody risk entirely. If your data classification level is high, this is worth the additional cost.
For detailed guidance, explore data destruction advice and learn how secure equipment recycling keeps both your data and your compliance posture intact.
Choosing certified vendors and performance benchmarks
Ensuring secure destruction is just one piece. Selecting the right certified vendors and understanding their performance benchmarks is where sustainable solutions emerge. Not all recyclers are equal, and stated recycling rates can obscure what is actually happening to your equipment downstream.
Here is what top-tier certified vendors look like by the numbers. Enterprise IT collection rates range from 80% to 99% with a median of 92%. Certified recycler material recovery sits between 85% and 97%, also at a 92% median. Refurbishment and reuse rates span 30% to 75%, depending on the equipment condition and vendor capabilities.
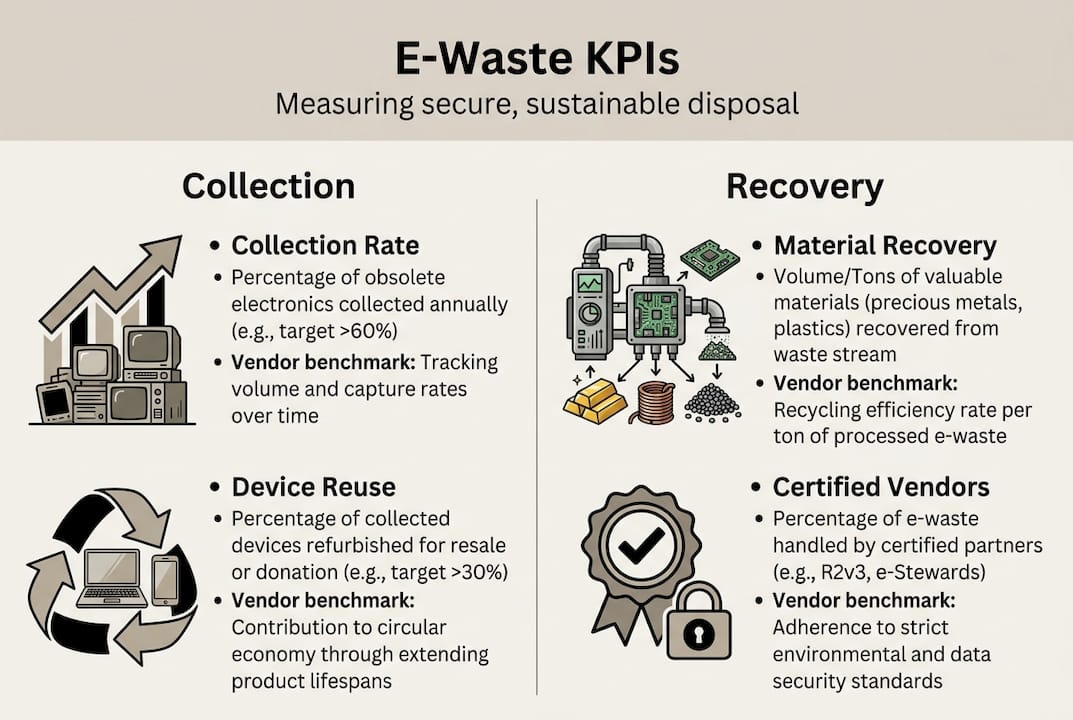
| KPI | Low end | High end | Median |
|---|---|---|---|
| Enterprise IT collection | 80% | 99% | 92% |
| Material recovery (certified) | 85% | 97% | 92% |
| Refurbishment / reuse | 30% | 75% | ~52% |
The two dominant certifications to evaluate are R2v3 (Responsible Recycling, version 3) and e-Stewards:
- R2v3 uses a risk-based approach. Vendors must address downstream risks but have flexibility in how they meet requirements.
- e-Stewards applies uniform, high-rigor standards with a stronger emphasis on closed-loop recovery and prohibiting export to countries without equivalent standards.
- Both require downstream tracking, but e-Stewards generally demands more documentation depth.
When evaluating vendors, ask for:
- Scope 3 ESG reporting support (can they provide data for your sustainability disclosures?)
- Annual audit results from independent third parties
- Downstream vendor lists so you can verify the full chain
For context on industry benchmarks for e-waste and e-waste recycling certifications, the certification alone is not enough. How a vendor performs against benchmarks tells you more than the logo on their website.
“A vendor’s certification is the floor, not the ceiling. Your due diligence starts there and goes much further.”
For eco-friendly IT asset recovery that meets both security and sustainability goals, benchmark performance and certification depth must align with your organization’s risk profile.
What most IT leaders miss about green e-waste management
Here is the uncomfortable reality: most vendor KPIs report by weight. A vendor can claim a 92% recycling rate and still send a significant share of recoverable materials to lower-quality processors. Reported recycling rates are often weight-based, not true closed-loop recovery, and the gap between those two figures runs 15% to 30% at many facilities.
This matters because your ESG reporting depends on accurate downstream data, not just collection totals. Scope 3 emissions tracking requires knowing where materials actually end up, not just where they were handed off.
The organizations doing this well share one habit: continuous downstream audits. They do not rely on annual certifications alone. They build audit rights into vendor contracts and exercise them. That practice catches process drift before it becomes a liability and generates the granular data that supports credible driving e-waste sustainability claims.
Transparency, not recycling rates, is the real differentiator when selecting a long-term ITAD partner.
Take the next step: Secure sustainable e-waste solutions
Your organization now has a clearer picture of what green e-waste management requires, from data destruction standards to vendor benchmarks. The next move is putting it into practice with a partner built for exactly this challenge.
UsedCartridge.com provides turnkey solutions for secure e-waste management that cover the full disposition cycle. Whether you need certified data destruction, e-waste recycling for business compliance, or responsible computer recycling for retiring IT fleets, the services are designed to meet your security and sustainability requirements. Request a free quote or schedule a pickup to start aligning your asset disposition process with the standards your organization deserves.
Frequently asked questions
What are the main steps in secure green e-waste management?
Steps include inventorying assets, applying certified data sanitization methods, selecting R2v3 or e-Stewards certified vendors, and verifying responsible downstream disposal with documented chain-of-custody records.
How do EPR regulations affect IT asset management?
EPR laws require producers to fund collection and recycling infrastructure, raising the compliance bar for businesses. With EPR enforced in 67 countries, IT teams operating globally must verify vendor registration across every jurisdiction where assets are retired.
What KPIs should organizations monitor for green e-waste management?
Priority KPIs are collection rates, material recovery rates, and device reuse percentages. Enterprise IT collection benchmarks run 80% to 99%, making collection rate the baseline metric for vendor evaluation.
What’s the difference between R2v3 and e-Stewards certification?
R2v3 applies a risk-based framework allowing vendors flexibility in meeting standards, while e-Stewards enforces uniform high-rigor requirements with stricter downstream tracking suited for organizations prioritizing closed-loop recovery and Scope 3 ESG accuracy.
